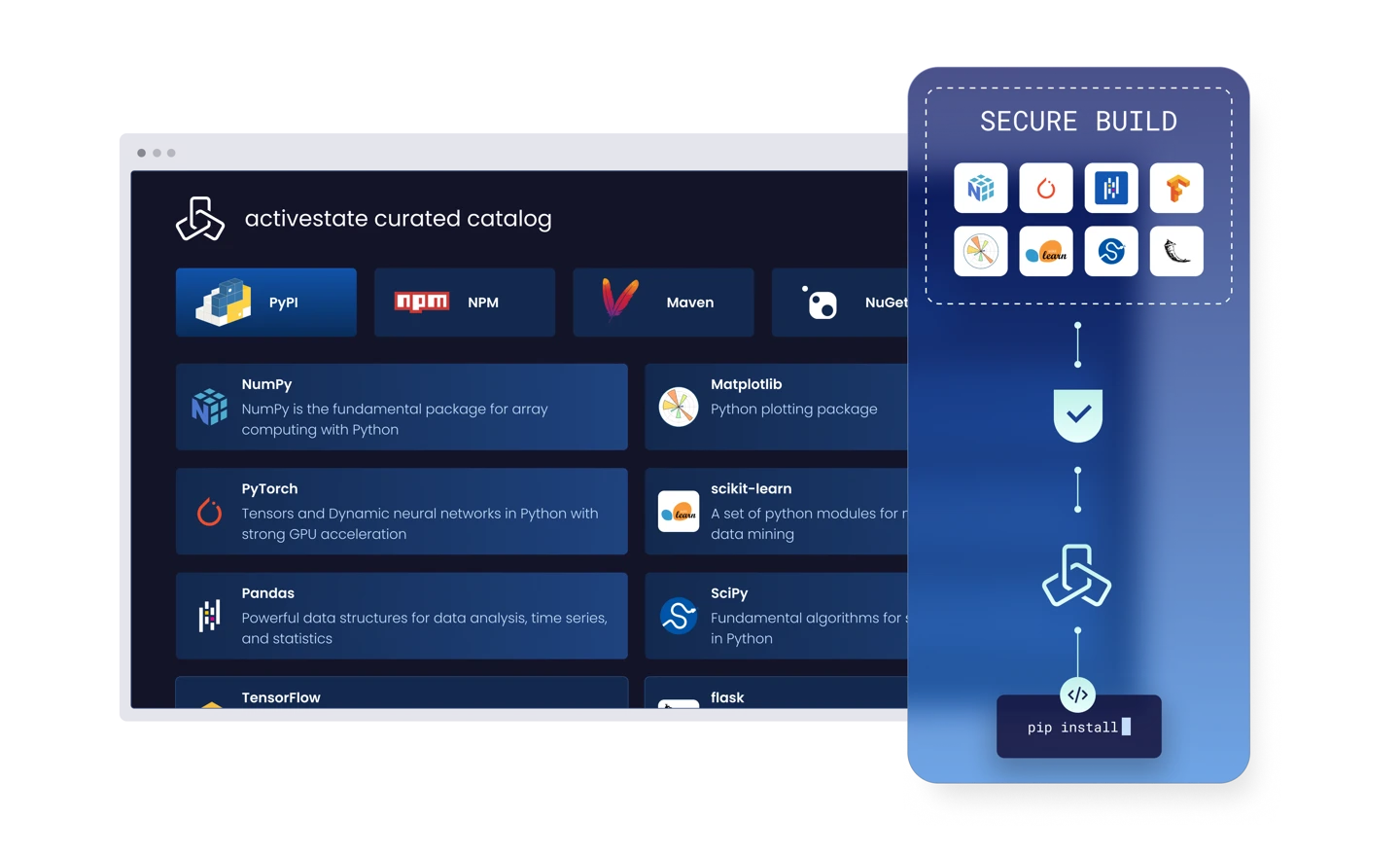
ActiveState Curated Catalog
What is an ActiveState Curated Catalog used for?
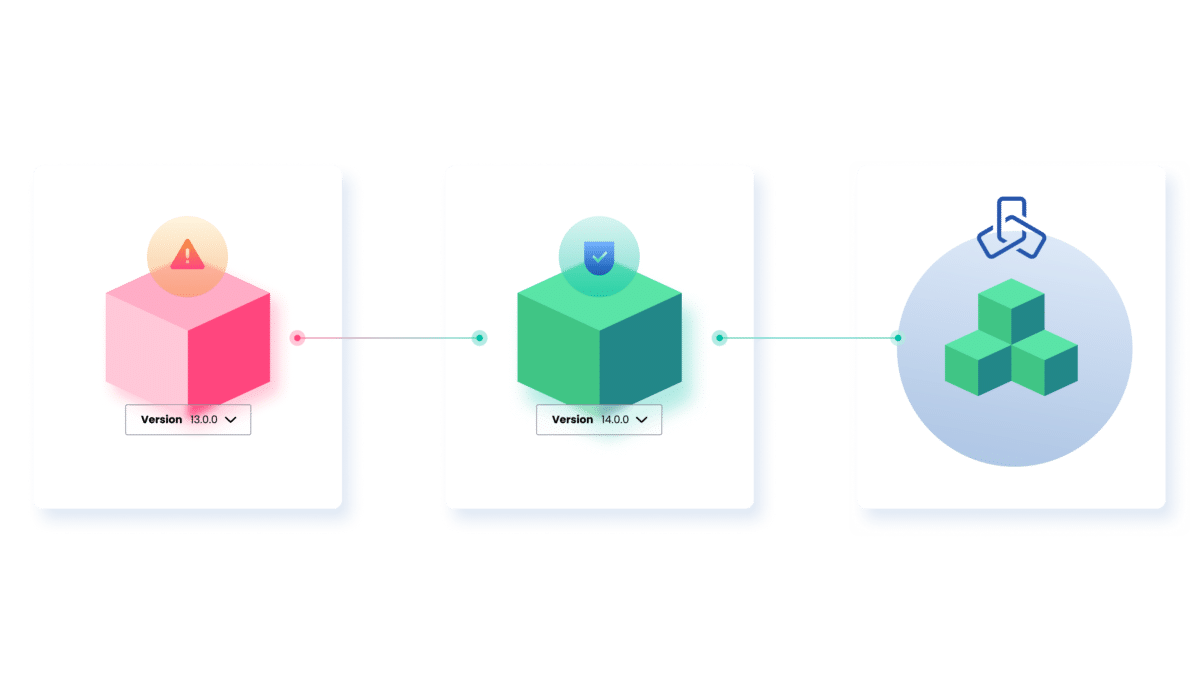
Secure your software supply chain
Replace unvetted and risky components before they reach developer or production environments with verified and continuously monitored components.
Centralize open source governance with low-friction guardrails
Guard how open source is selected and approved for use within your organization without introducing additional friction. Transform security policies from blockers into enablers.
Simplify open source compliance
Compliance audits are made easy with complete visibility into open source usage across your organization, including who approved it and why it’s safe. Compliance reporting moves from weeks to hours.
Reclaim hours lost to development toil
Replace hours spent on manual open source remediation tasks with time spent on new development. Engineers focus on development velocity instead of firefighting vulnerabilities.
Why deploy an ActiveState Curated Catalog?
An ActiveState Curated Catalog provides security teams total control over what comes into their environments while giving engineering teams a fast and secure way to get what they need to build, onboard, and start new projects.
Vetted, built-from-source components
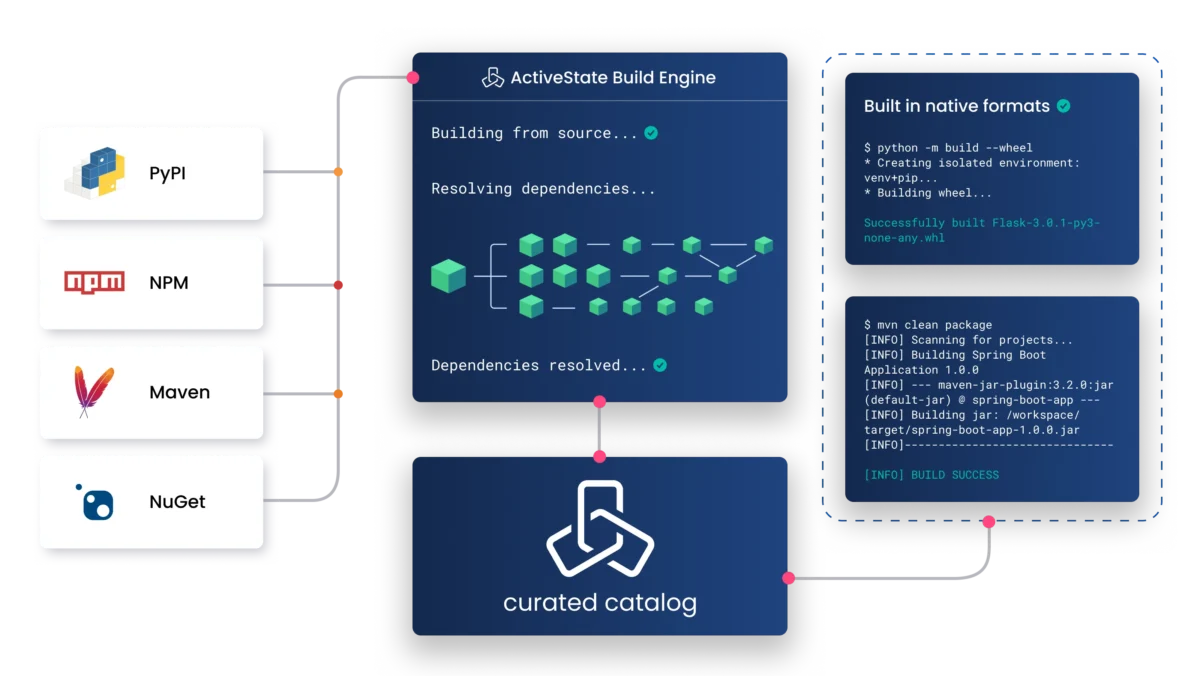
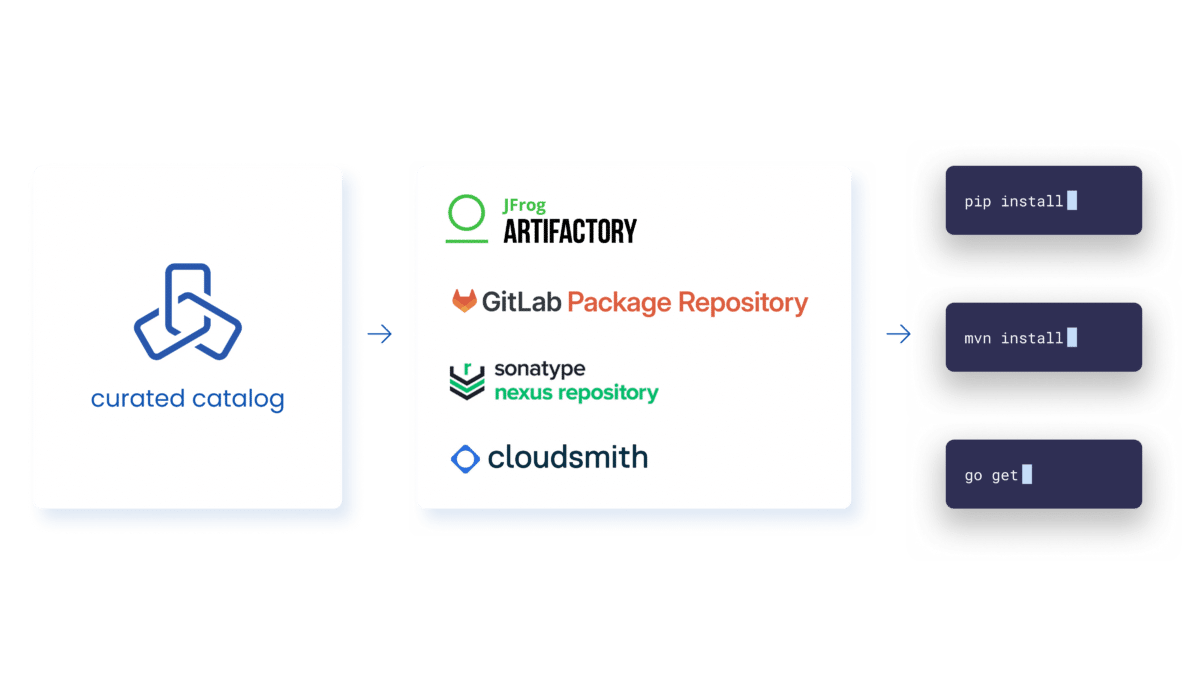
Secure artifact injection into native ecosystems
Component-level security feed
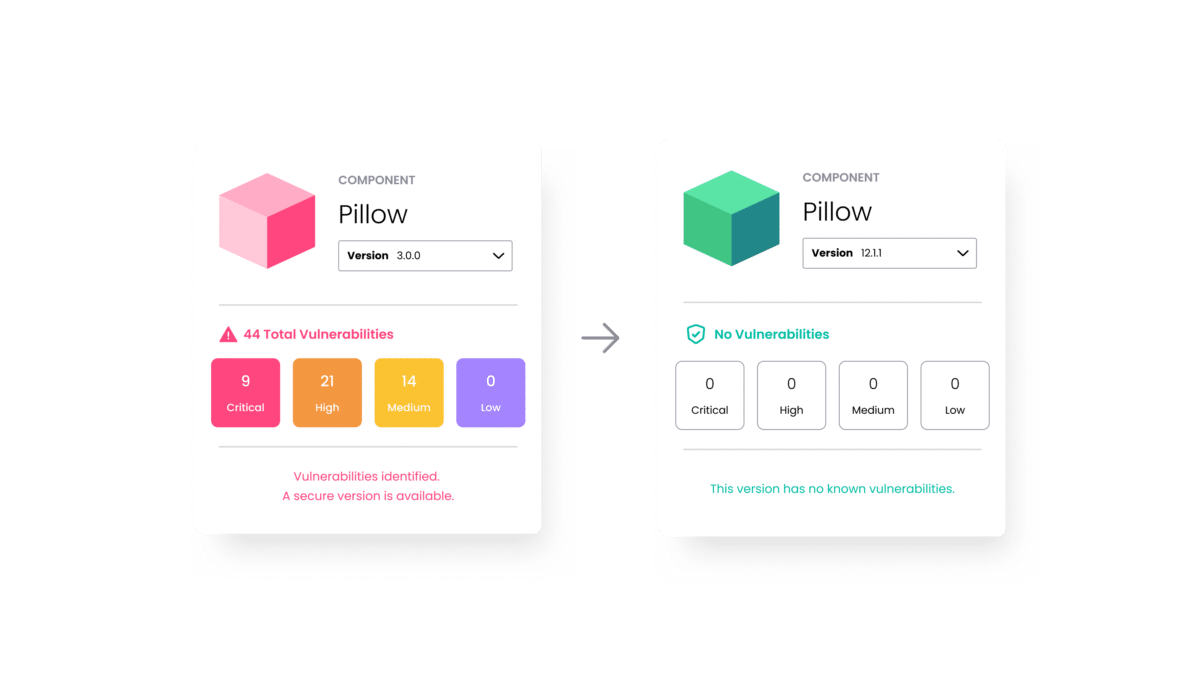
Fully remediated for you
FAQs
How does the ActiveState Curated Catalog work with my existing tools?
Will this slow down my developers?
What languages are supported?
The catalog supports more than 12 language ecosystems, including Python, Java, JavaScript, C Libraries, and R, providing a unified solution for engineering teams using multiple open source languages.



